Phone Lookup Explorer Start 908-829-0335 Revealing Trusted Caller Signals
Phone Lookup Explorer examines how trusted signals shape caller legitimacy, focusing on verifiable badges, IDs, and contact quality metrics. It highlights rapid, data-backed checks and anomaly detection to inform real-time trust judgments. Privacy-conscious tools and cryptographic attestations guard exposure while user-defined whitelists guide interpretation. The framework promises transparency without overreach, yet the balance between openness and safeguards remains a nuanced question for practitioners to confront.
What Phone Lookup Explorer Reveals About Trusted Callers
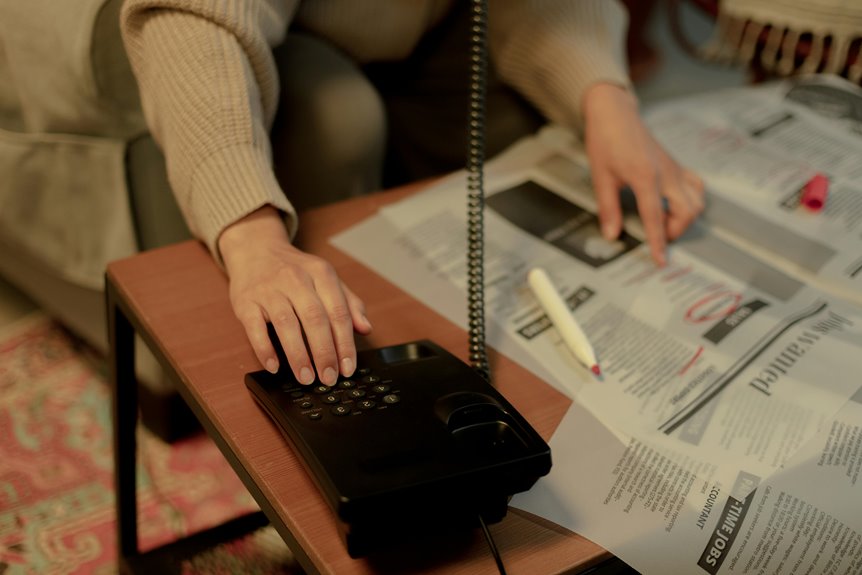
Phone Lookup Explorer sheds light on how trusted callers are identified by compiling signals from caller history, authentication checks, and user-defined whitelists.
The system emphasizes trusted caller status through verification signals and contact quality metrics, presenting a concise view of caller legitimacy.
Privacy tips accompany data, ensuring responsible use while maintaining freedom to decide trust boundaries.
Spotting Verified Signals: Badges, IDs, and Contact Quality
Spotting verified signals hinges on clear indicators such as badges, IDs, and measurable contact quality metrics. The analysis emphasizes badge signals and id verification as objective cues, not mere aesthetics. Data-driven benchmarks assess response time, consistency, and reliability across verified profiles. This approach supports freedom-seeking readers by prioritizing transparent, reproducible signals over ambiguous trust impressions.
Quick Checks to Evaluate Caller Trust in Real Time
Quick checks to evaluate caller trust in real time employ rapid, data-backed signals that can be observed during an inbound call.
The approach emphasizes a trusted caller’s behavioral cues, call-origin metadata, and anomaly detection, yielding immediate indicators for decision-making.
Real time evaluation supports prudent engagement, reducing risk while preserving caller autonomy and privacy in a freedom-valuing communications landscape.
Tools and Tips to Verify Messages Without Compromising Privacy
Tools and tips for verifying messages without compromising privacy center on privacy-preserving checks that minimize exposure of sensitive data while maximizing message authenticity. The approach highlights trusted contact references and robust verification signals, leveraging metadata minimization and cryptographic attestations. Readers gain data-driven guidance for independent validation, balancing freedom to communicate with disciplined caution, ensuring source credibility without unnecessary disclosure.
Conclusion
Phone Lookup Explorer distills trust into measurable signals—badges, IDs, contact quality metrics—enabling real-time, data-driven trust assessments. The toolkit emphasizes privacy-conscious verification, cryptographic attestations, and user-defined whitelists to minimize exposure while maintaining transparency. With anomaly detection and call-origin metadata, it translates complex signals into practical insights for evaluating legitimacy. In short, trust is a beacon forged from verifiable data, guiding user decisions without sacrificing privacy, like a lighthouse in data fog.




